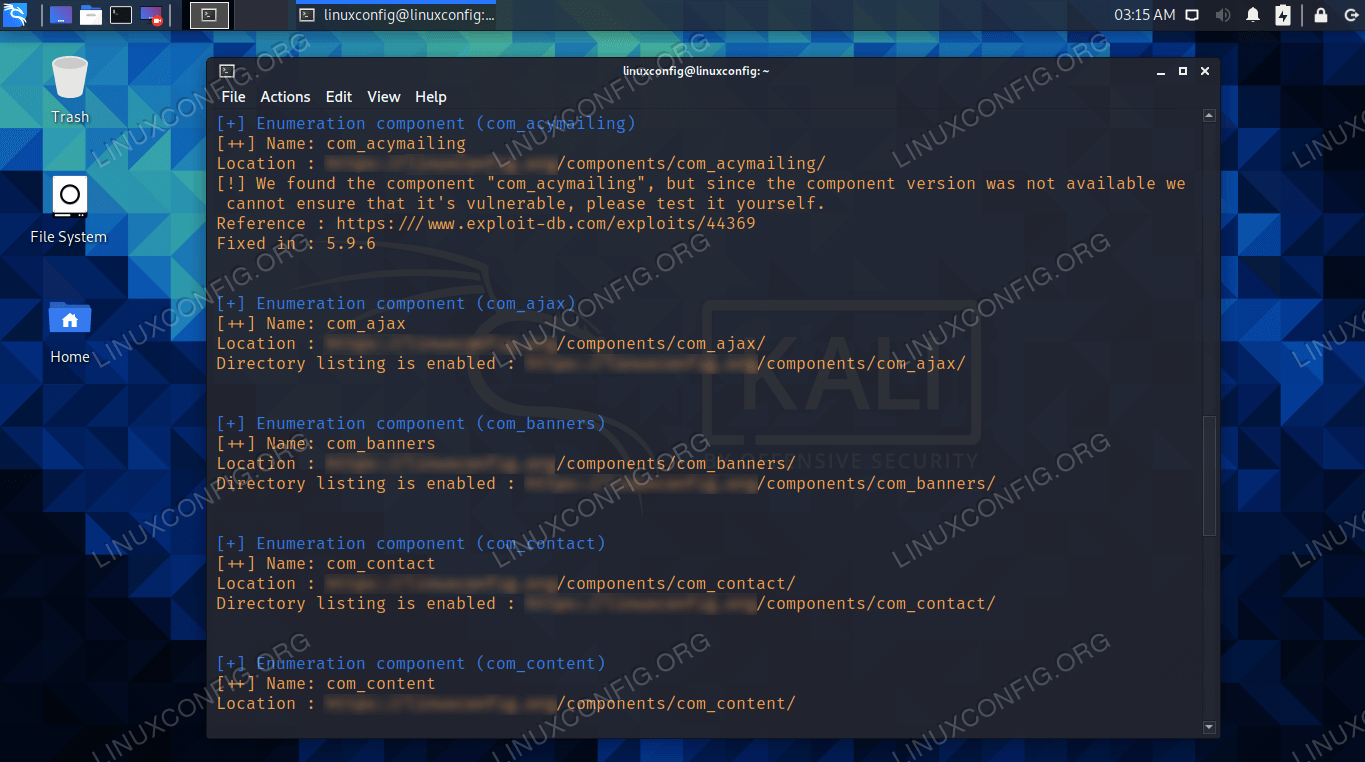
Use JoomScan to scan Joomla for vulnerabilities on Kali - Linux Tutorials - Learn Linux Configuration

Richard is working on a web app pen testing assignment for one of his clients. After preliminary information, gathering and vulnerability scanning Richard runs the SQLMAP tool to extract the database information.